Since the start of 2021 we have witnessed an increase in Ransomware activities in Ireland in particular targeted “double exploit” campaigns. Of note are the Ryuk and Conti variants. Conti being a newer more advanced version of Ryuk. The Ryuk variant has been used in attacks on 3rd level institutions. The Conti variant has been used in the recent HSE and Department of Health attacks.
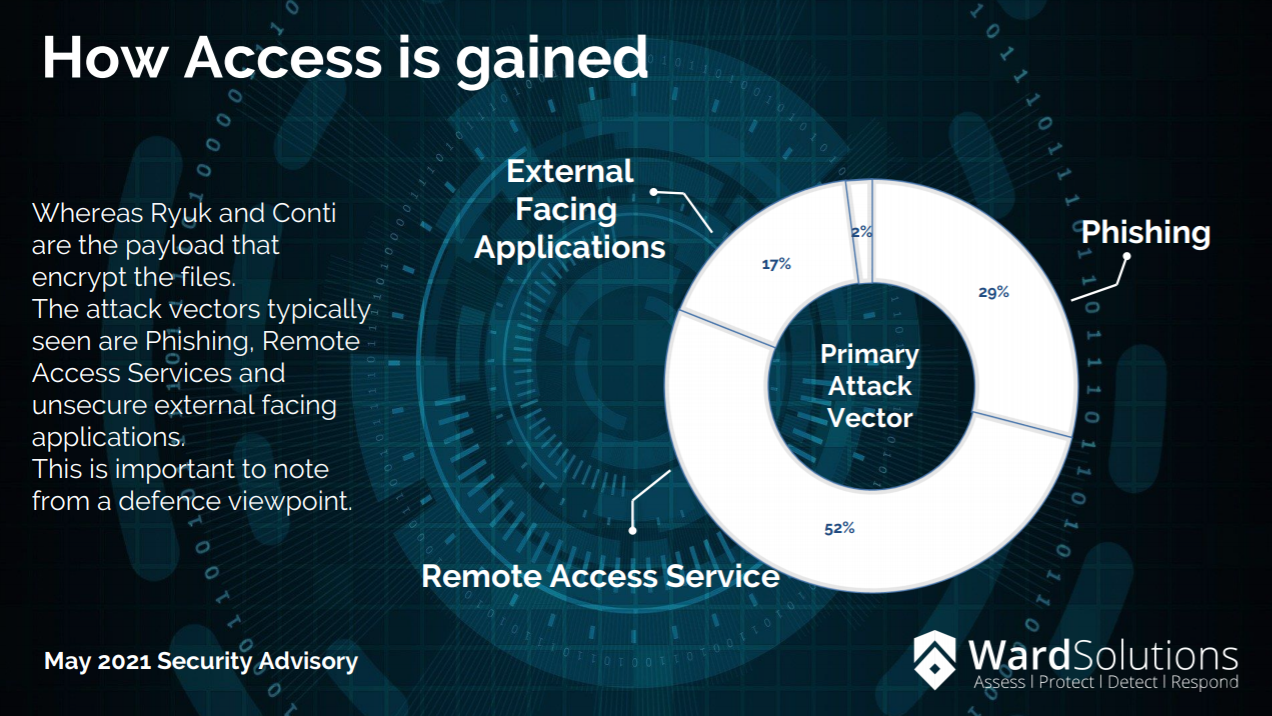
Although these attacks have highlighted the threat of Ransomware it should be stressed that Ransomware represents an ongoing threat. It is believed that the same threat actor group WIZARD SPIDER are responsible for Ryuk and Conti based attacks. In 2019 this group was able to extort approximately $60 million in bitcoin. Other Ransomware variants of note are Sodinokibi and Lockbit.
Because of the current landscape we have compiled our Top 13 Key Steps to take to Protect Against Ransomware.
- Educate your c-suite and board
- Deliver and confirm Security Awareness Training
- Create, maintain and regularly test a cyber incident response plan, with Ransomware specific playbooks.
- Perform, test and secure Backups on a regular basis.
- Conduct regular vulnerability scans and address vulnerabilities in particular those on externally focused assets.
- Regularly patch and update software.
- Ensure devices from endpoint to cloud are securely configured.
- Implement Next Generation Endpoint Protection (EPP) and Endpoint Detect and Respond (EDR) solutions.
- Implement network segmentation
- Implement secure remote access solutions using VPN, ZTNA and SASE solutions. Ensure all remote access requires a minimum 2FA authentication.
- Implement secure mail gateways, incoming mail controls and URL click protection.
- Implement a centralised security operations and management approach through a Security Operations Centre (SOC)
-
Secure and harden your Active Directory to minimise the risk of bad actors gaining escalated privileges to your servers and domains. Monitor administrator access continuously. Ensure your Active Directory is backed up and that at least 1 of these backups is offline and inaccessible to an attacker
Following these tips will help you and your institution stay Cyber Threat aware. If you would like more information, you can talk to one of our specialists today and you can download our Information Security Guide below.