Security Advisory Update – Critical Processor Flaws Update Issued by Ward Solutions Security Operations Centre Updated January 11, 2018
Further to our recent advisory on the major flaws identified in a range of widely used chipset, further information has been released with regard to various technologies and mitigation of these vulnerabilities.
What are the Flaws Identified?
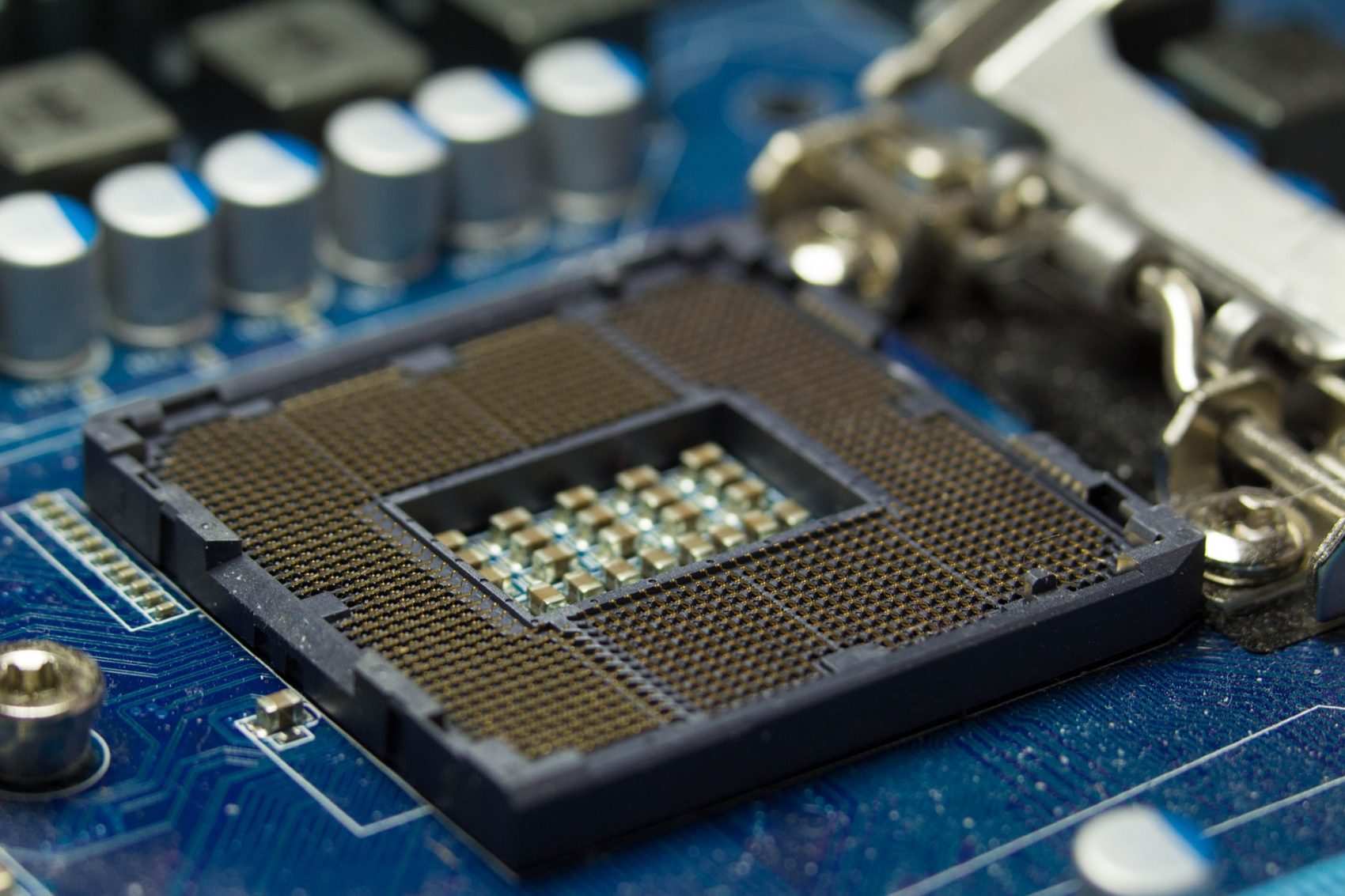
The flaws, which are believed to be present in all modern processors produced in the last ten years, allow low-privileged processes to access memory in the computer’s kernel. The implications of these flaws are far-reaching and will impact not just Linux, Windows, and MacOS but also virtual and cloud environments. There have also been reports predicting up to a 30 percent degradation in performance as a result of mitigation of the vulnerabilities. 1 The researchers involved in the discovery of these flaws, including Google’s Project Zero, identified three vulnerability variants;
CVE-2017-5715: Elevation of privilege / information disclosure vulnerability. Through exploitation of this vulnerability, an attacker could infer data values from memory which would normally be inaccessible to the user due to permissions.
CVE-2017-5753: Exploitation of this vulnerability is based on the ‘speculative execution’ used by the Intel chip to attempt a ‘pre-execute’ of code to retrieve kernel memory. Intended as a performance enhancement feature, this design flaw could be exploited by an attacker to cause the CPU to load from an untrusted location.
CVE-2017-5754: This vulnerability could allow an attacker in user space to access memory in kernel space without the usual permission checks, relying on the fact that the CPU may opt to validate permissions for access to memory locations at a later stage. 2
The flaws in the chips leading to the aforementioned potential exploits have been dubbed ‘Spectre’ which affects chips from many vendors and ‘Meltdown’ which appears to affect only Intel chips.
How do I Remediate?
While Intel and other chip vendors will likely address the flaws in the future manufacture of chips, users need to take action to protect devices which are currently using the chipsets. Numerous vendors have been working on remediation plans to date.
Microsoft: Plans to release necessary updates to Windows OS in the upcoming Patch Tuesday
Microsoft has announced that they will be deploying mitigations to cloud services. Azure platforms are scheduled to undergo maintenance including reboots on January 10th, it is expected that this is part of Microsoft’s remediation plan.
Microsoft has already released updates to Internet Explorer and Edge.
Amazon EC2: Amazon has confirmed that it’s AWS instances are protected, however, it is recommending that customers patch their operating systems.
Google: Google has confirmed all Android devices with the latest security update are protected.
Google Chrome browser, Chrome 64, scheduled for release on January 23rd, will protect against this exploit.
Google has confirmed all versions prior to 63 are not patched, however, Chrome OS 63 which includes mitigation protection received a widespread release on December 15th, 2017.
Google has confirmed its Cloud Infrastructure is protected, however, for its Compute Engine, Google is recommending customers update their VM operating systems. 3
RedHat: RedHat is recommending that customers patch immediately. A full listing of version and vulnerability to each of the identified variants have been published. Please refer to this listing for full details. 4
Cisco: Cisco has released a list of under investigation, unaffected and affected products along with expected release dates for patches to resolve if applicable. Cisco devices are considered potentially vulnerable only if they allow customers to execute their customized code side-by-side with Cisco code on the same microprocessor. 5
Checkpoint: Checkpoint has rated this as a Low risk to their devices as it would require root level
privileges to run on their OS. Checkpoint will release a patch only when they are sure of its effect on quality and performance. 6
Juniper: Juniper has rated the risk level as low on Juniper OS devices. In the case of Junos OS, in
order to exploit this vulnerability, an attacker must have a local authenticated privileged (admin) and needs to bypass the image validation checking. 7
Fortinet: Fortinet is actively conducting an extensive review to determine the potential
impact to Fortinet solutions, and at this time has classified the risk to Fortinet products as low. An attack is only possible on devices when combined with an additional, unrelated local or remote code execution vulnerability.8
Debian: A patch has been released to remediate the Meltdown attack. This solution may impact on performance. At the time of this update, there is no patch release for Spectre and this is expected to be addressed in a later update.9a, 9b
VMware: VMware is recommending that customers patch immediately. A full listing of version and vulnerability to each of the identified variants have been published. Please refer to this listing for full details. 10
For detail on other vendors, please refer to their individual security advisories.
How Can Ward Help?
For Managed Service customers, the Ward Support team will be reviewing individual environments and making recommendations on appropriate patching for all supported devices.
For all other customers, if you would like additional information or would like support in assessing and protecting your environment, please contact info@ward.ie or your account manager, as appropriate.
Further reading:
3 https://support.google.com/faqs/answer/7622138#chrome
4 https://access.redhat.com/security/vulnerabilities/speculativeexecution
7https://kb.juniper.net/InfoCenter/index?page=content&id=JSA10842&cat=SIRT_1&actp=LIST
8 https://blog.fortinet.com/2018/01/04/fortinet-advisory-on-new-spectre-and-meltdown-vulnerabilities
9a https://www.debian.org/security/2018/dsa-4078
9b https://security-tracker.debian.org/tracker/source-package/linux
10https://www.vmware.com/us/security/advisories/VMSA-2018-0002.html