Cyber Security Awareness Month takes place in October of every year. The objective of this initiative is to raise awareness of the cybersecurity threats to citizens and ultimately a business.
Cybersecurity is integral in every business!
In the next fours weeks, we will be releasing a set of questions on security. Last week we released two questions, here are the answers.
The first question in the series was:
Why should an enterprise perform a penetration test?
A penetration test is conducted to evaluate the security of an IT infrastructure to identify all vulnerabilities within the enterprise. These vulnerabilities may exist in operating systems or may occur due to improper configurations or risky end-user behaviour.
Penetration tests must be conducted more than once a year to ensure a business runs smoothly without any risks involved. Even a vulnerability scan can help by alerting security teams with the discovery of all your vulnerabilities. Here is the link to our blog on the difference between a pen-test and a vulnerability scan, click here

The second question in the series was:
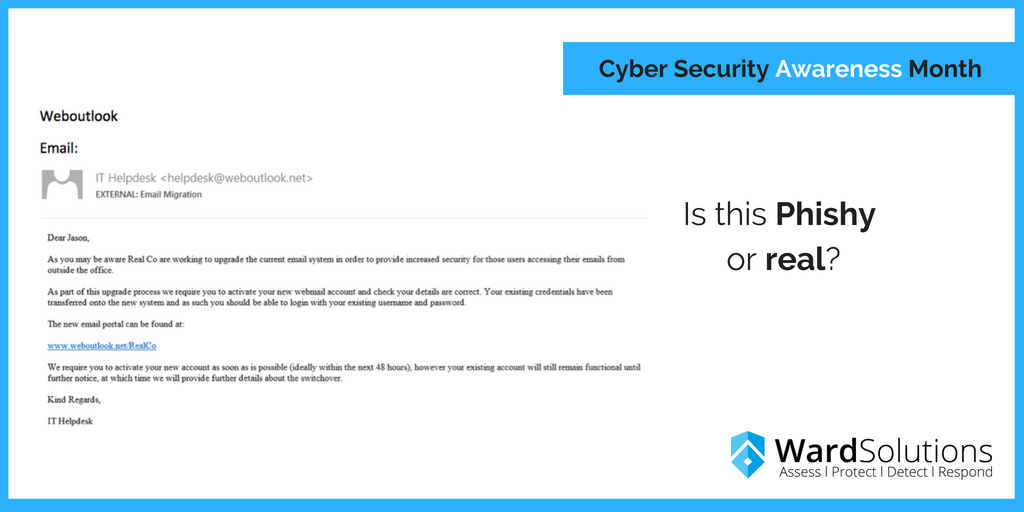
Is the below e-mail Phishy or real?
The below e-mail is clearly a phishing scam, they aren’t asking for a transfer but they have inserted a link which is clearly malicious. What tends to happen is that if an
e-mail asks for a transfer of money employees suspect that this is a phishing scam but when they see an e-mail like this, employees fall for it since it looks so real. This kind of scenario can be avoided by training employees to read through the e-mail carefully and if they are not sure, immediately forward it to the support team just to be on the safer side.
Here’s a quick recap to one of our Ward Infosec blog on phishing, click here.
Another thing we’re starting in this series is, we’re picking three best quotes from industry experts on the cybersecurity world we are living in today.
Cybersecurity is a shared responsibility and it boils down to this: In cybersecurity, the more systems we secure, the more secure we all are. – Jen Johnson
For every lock, there is someone out there trying to pick it or break in. – David Bernstein, President at Bernstein agency
There are only two types of companies:
Those that have been hacked, and those that will be. – Robert Mueller, FBI Director 2012
E-mail us at info@ward.ie or call 1800 718 850 to discover our range of information security solutions and discuss your unique requirements with one of our security experts.